It is critical that an organisation secures all of their assets along their entire software supply chain. For instance, in a DevOps lifecycle, as a developer, ensuring the security and stability of your code is crucial. One effective way to do this is by implementing automated security testing as part of your continuous integration and deployment (CI/CD) pipeline.
In this blog, we will explore how to use Nuclei, a powerful open-source tool for scanning web applications, in your GitHub CI/CD pipeline.
What is a GitHub CI/CD?
GitHub Actions is a suite of tools that enables developers to build, test, and deploy their code directly from the GitHub platform. Using this, the developers can set up a CI/CD pipeline that automatically builds, tests, and deploys their code every time they push changes to their repository. This helps to ensure that code changes are automatically tested and deployed consistently and reliably.
Often organizations have shifted to the DevSecOps model, where they integrate security right within the CI/CD pipeline. While this is a good approach to ensure security defense-in-depth and early mitigation, it is also essential to run periodic scans on the live version of the product, such as an API or a web application endpoint. Running an automated scan from a black box perspective is no longer a tedious task with the help of Nuclei.
Nuclei - A fast & customizable vulnerability scanner
Nuclei is an open-source tool for scanning vulnerabilities with the help of pre-defined templates written in YAML. It can scan any vulnerability class, including cross-site scripting (XSS), SQL injection, and remote command execution. Nuclei is fast and efficient, making it a powerful tool for identifying potential application vulnerabilities.
It can be set up to run in an internal network environment for local and publicly deployed applications.
Power of Nuclei
One of the key benefits of Nuclei is their ability to scan a wide range of vulnerabilities quickly and accurately. It uses pre-defined templates, called "rules," to scan for known vulnerabilities, and it can also be customized to scan for specific vulnerabilities or issues. This makes it an ideal tool for identifying potential vulnerabilities in your web applications.
Now, let’s jump back to the original discussion and understand how to integrate nuclei in your CI/CD pipeline.
Integrating Nuclei in CI/CD pipeline
Integrating the nuclei scanning capabilities into your CI/CD pipeline is quite straightforward. We will create a private repository on GitHub and assume it hosts code for a public web application application, say http://testphp.vulnweb.com/.
Follow the below steps to set up a CI/CD pipeline in GitHub and run a workflow to launch Nuclei Scan on testphp.vulnweb.com with every code change.
- Login to GitHub web application.
- Click on the + Icon in the top right corner and select New Repository.
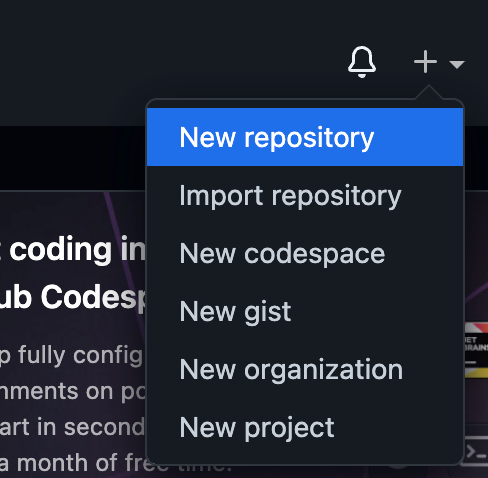
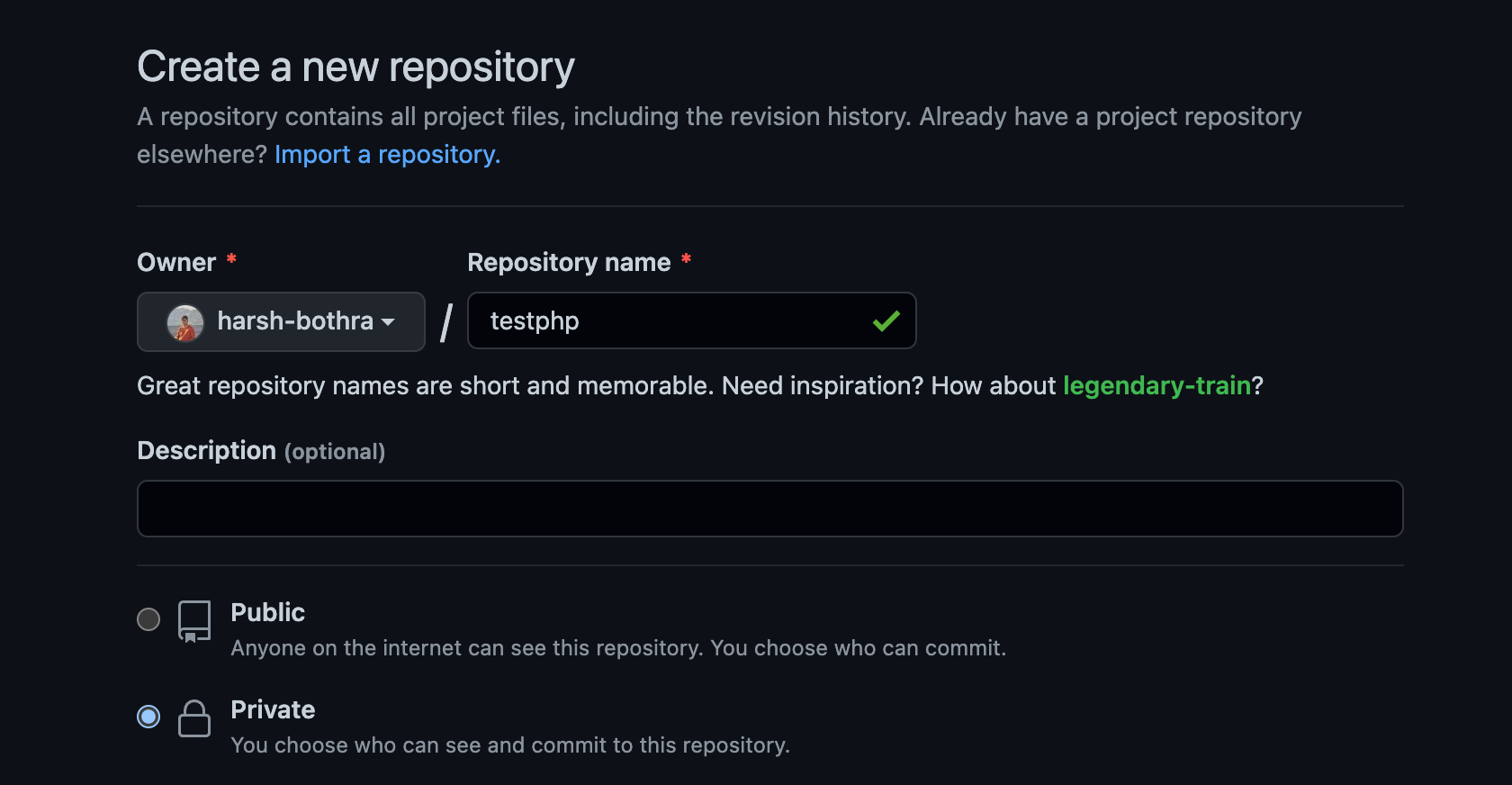
3. Create a new repository with any name and make it private.
4. Now, using either GitHub Desktop or Git CLI, clone the repository locally on your system.
5. Navigate to your repository folder and create a new directory: .github/workflows/
6. Now create a .yml workflow file in this directory with the following workflow code:
name: CI
on: [push]
jobs:
build:
runs-on: ubuntu-latest
steps:
- uses: actions/checkout@v2
- name: Run Nuclei
uses: projectdiscovery/nuclei-action@main
with:
target: "http://localhost"7. Change the target: parameter to your application URL. It also supports multiple URLs. This workflow will run the Nuclei Action created by the ProjectDiscovery team to run nuclei on your defined target URL(s). Detailed documentation on Nuclei GitHub Action can be found here: https://github.com/projectdiscovery/nuclei-action
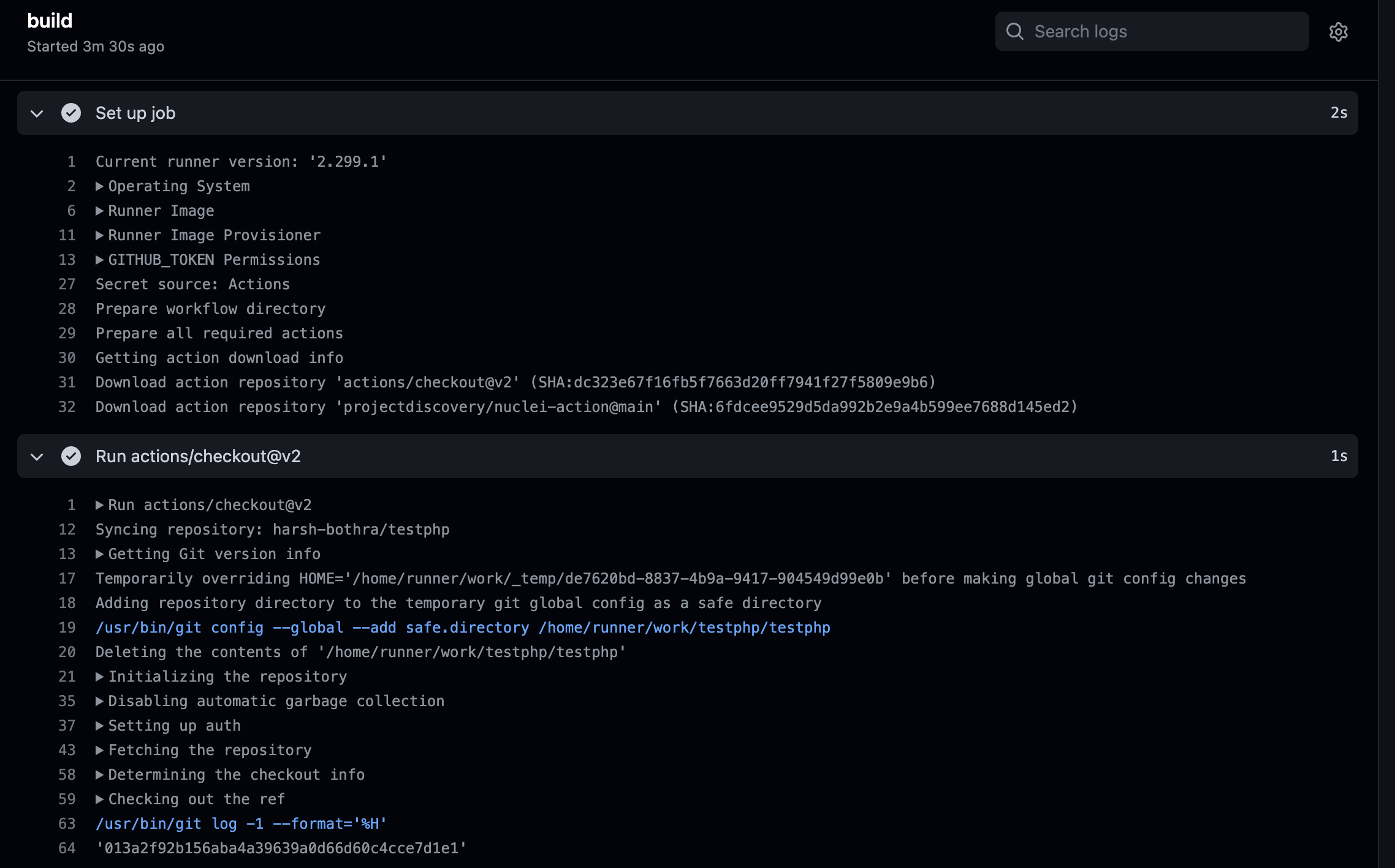
8. Now, push the code back to the repository using Git CLI or GitHub Desktop and navigate to your repository to see the workflow start executing.
Performing Regression Testing with Nuclei Custom Templates
Keeping track of known vulnerabilities and ensuring that they are properly remediated is an essential task for any organization. With the constant evolution of technology and the frequent release of new code, it is crucial to perform regular regression testing to ensure that vulnerabilities are not reintroduced. However, this can be a tedious and resource-intensive task that can impact release schedules.
Fortunately, there is a solution that can streamline this process and make it more efficient. Nuclei is a powerful tool that allows organizations to perform regression testing using custom templates. By writing templates that specifically target known vulnerabilities, organizations can easily scan their code for any potential issues.
The process of writing templates for Nuclei is straightforward and user-friendly. Nuclei provides a comprehensive guide on its website that walks users through the process of creating templates. This guide can be found at https://nuclei.projectdiscovery.io/templating-guide/.
Let's dive into how custom templates can be utilized in the CI/CD pipeline to perform regression testing. By incorporating custom template scanning into your workflow, you can easily scan for known vulnerabilities and ensure that they are properly remediated with every code change.
To implement this feature, simply replace the code in your workflow file with the following instructions:
name: CI
on: [push]
jobs:
build:
runs-on: ubuntu-latest
steps:
- uses: actions/checkout@v2
- name: Run Nuclei
uses: projectdiscovery/nuclei-action@main
with:
target: ‘http://testphp.vulnweb.com/’
templates: custom_template_path
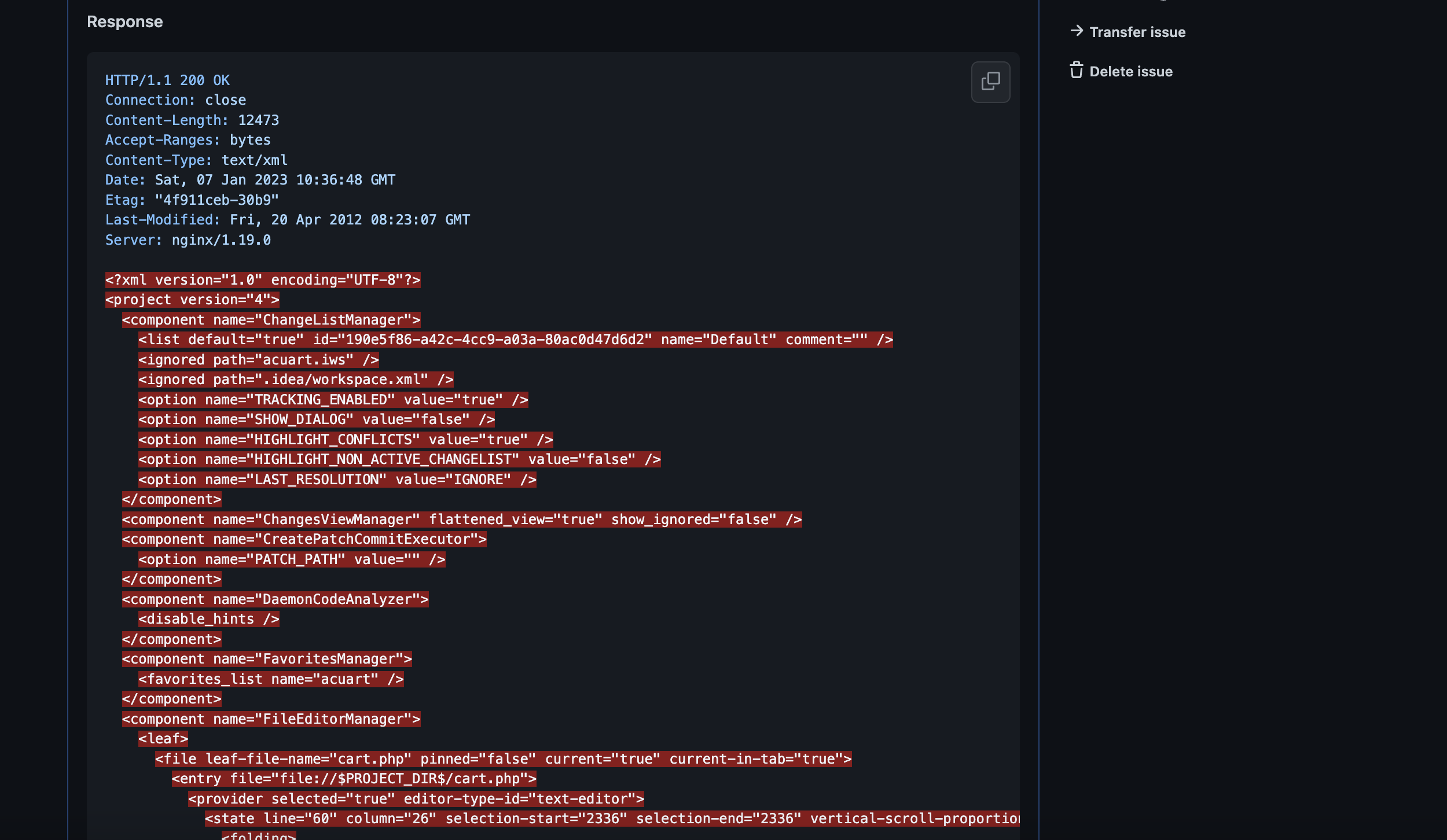
Automatic issue reporting using Nuclei scan results
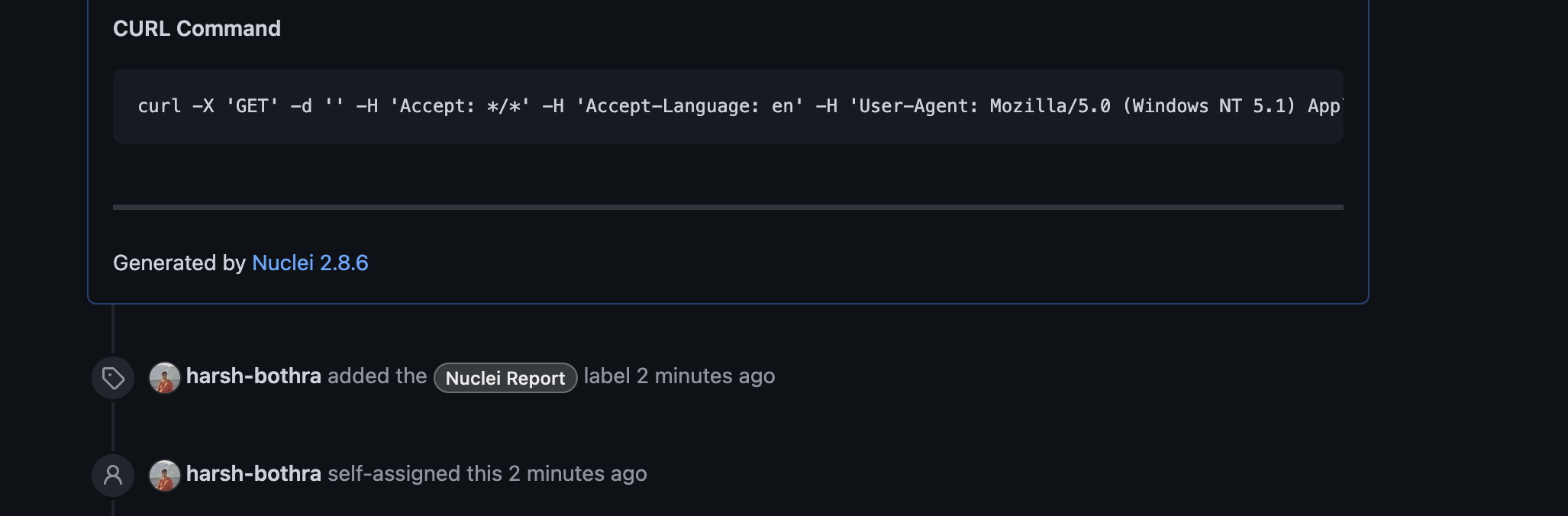
Once Nuclei has completed its scan, it is important to report any identified issues and notify the relevant parties. This can be done using a tool like GitHub Issues, which allows you to create and track issues within your repository.
Nuclei Action supports reporting the issues on GitHub Issues and GitHub Security Dashboard, making it easy to create a workflow.
In the above workflow file, replace the code with the following:
name: CI
on: [push]
jobs:
build:
runs-on: ubuntu-latest
steps:
- uses: actions/checkout@v2
- name: Run Nuclei
uses: projectdiscovery/nuclei-action@main
with:
target: ‘http://testphp.vulnweb.com/’
github-report: true
github-token: ${{ secrets.GITHUB_TOKEN }}
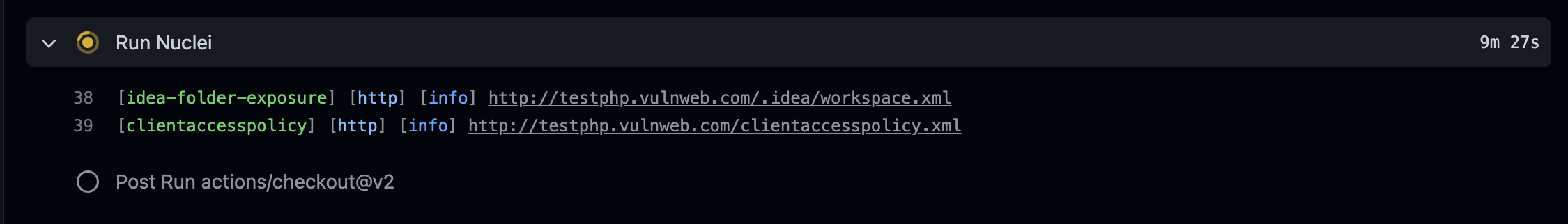
Commit the new changes, and you should see it will start a new workflow process, and at the end, it will report the issues. The reported issues can be found in the Issues tab.
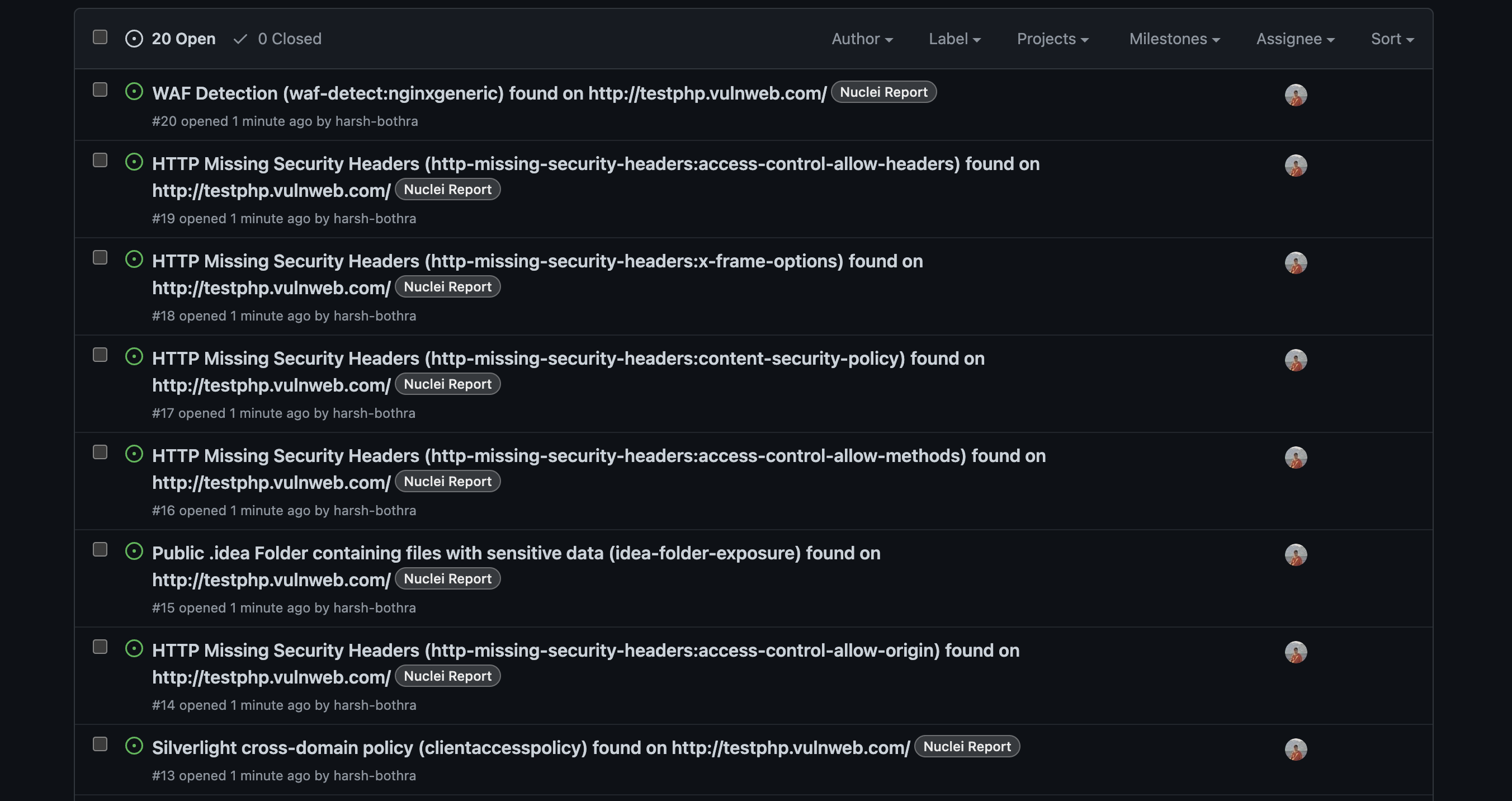
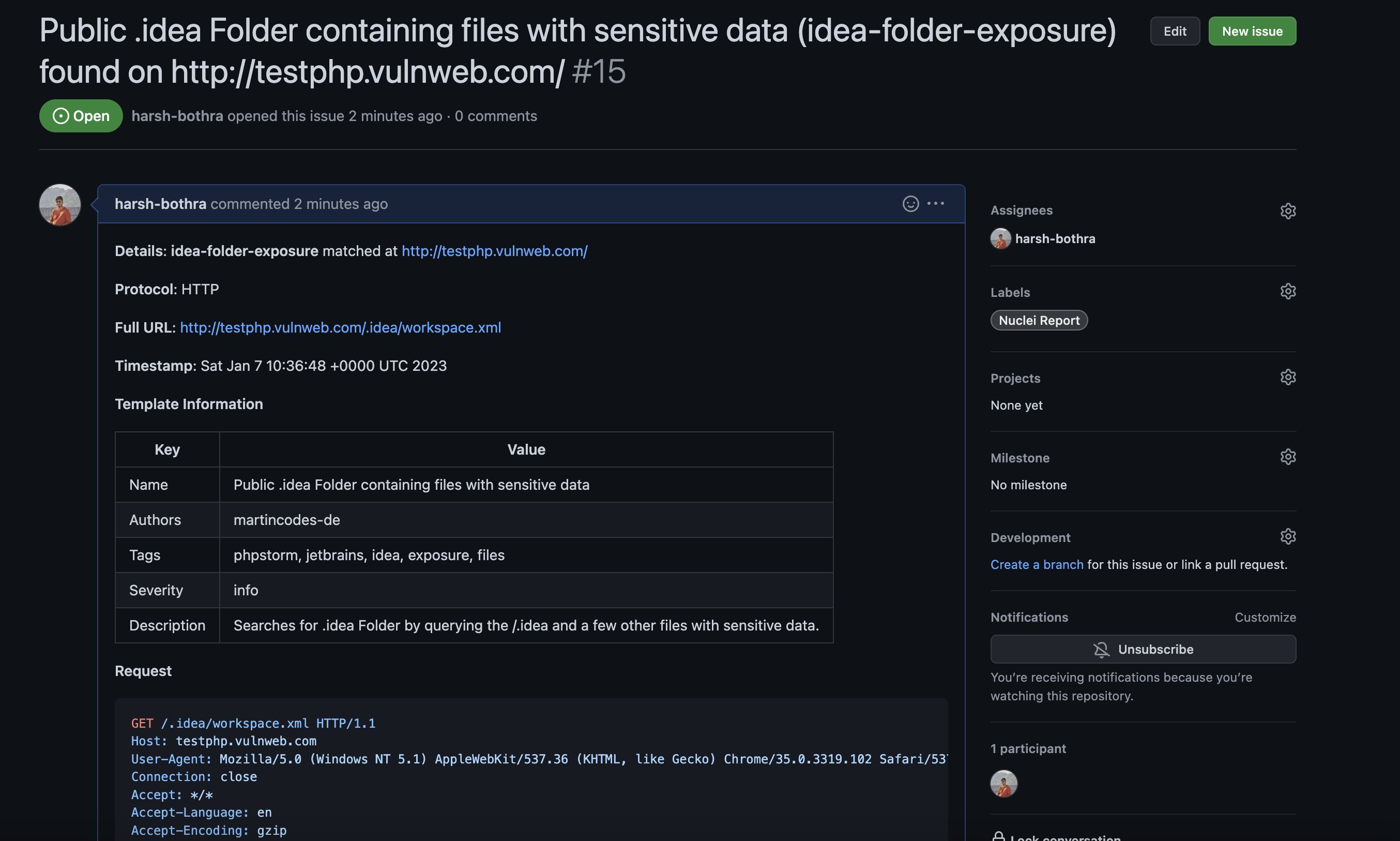
Similarly, if you already have a code repository, all you need to do is configure the workflow file as per your requirement and you are all set to scan whenever you commit a code change, your live application will be scanned using Nuclei and results will be reported as well.
Conclusion
Nuclei is an invaluable resource for anyone looking to ensure the security and stability of their web applications. Not only is it a powerful tool for identifying vulnerabilities, it is also open-source and easy to integrate into your GitHub CI/CD pipeline. It's important to remember that once you have identified any issues with Nuclei, you should notify the relevant parties so that they can be properly addressed. This will help to protect your web applications and the sensitive information they contain. Happy hacking!
- Harsh Bothra (@harshbothra_)